A database for red teaming, penetration testing, and ethical hacking resources

Sherlock is an OSINT tool for finding usernames across social networks to support digital investigations and reconnaissance.

ShipSec Studio is an open-source security workflow orchestration platform designed for building, executing, and monitoring automated security workflows at scale.
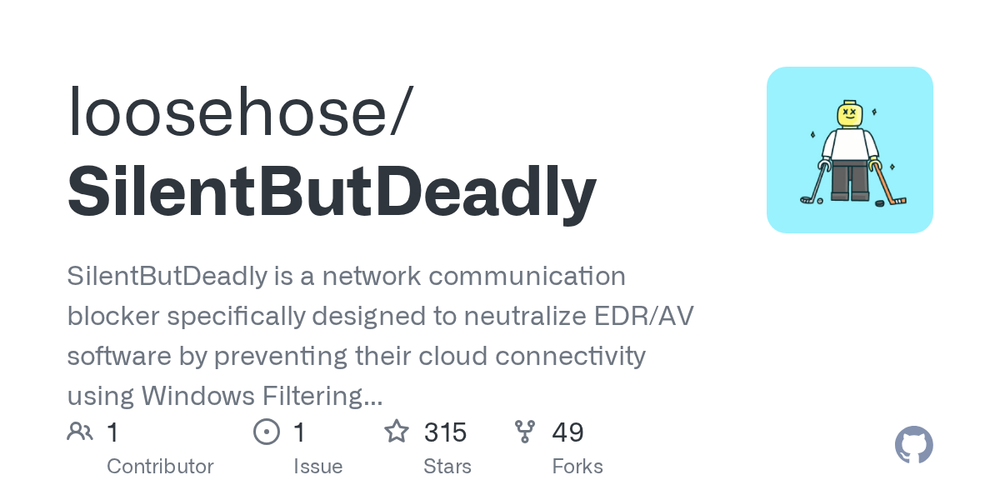
A network communication blocker designed to neutralize EDR/AV software using Windows Filtering Platform (WFP).

Snaffler is a pentesting tool to find credentials and sensitive data in Windows/AD environments by enumerating file shares and content.